I spent hours trying to figure out why I couldn’t connect my Galaxy S7 onto my Synology using a PPTP VPN on the Proximus 3G/4G Network (Belgium) while it was working fine if connected via WiFi.
Finally, I gave up and configured a L2TP/IPSec VPN. This one worked immediately like a charm, both on WiFi and 3G/4G. I am quite sure this is due to Proximus configuring my profile to use CGN (Carrier Grade NAT).
Click to Read More
I was initially inspired by this post (“Using Synology DiskStation as a VPN server using built-in Android VPN client”). So;
- I did first configure my Synology VPN Server to use PPTP as explained here (Official Knowledge base Synology)
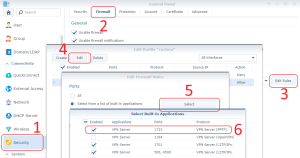
- Next, I did open my Synology Firewall (port 1723 for PPTP) via the Control Panel > Security > Firewall > Edit Rules > Edit an entry to Allow > Select Built-in applications > VPN Server (PPTP)
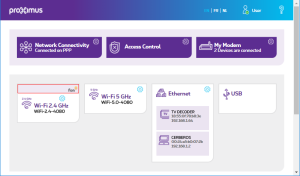
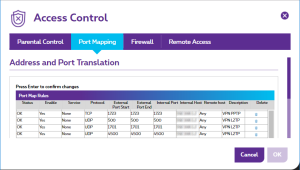
- Then, I did configure my Modem to route the TCP port 1723 to my NAS via Access Control > Port Mapping
- Finally, I configured a PPTP VPN on my Galaxy S7 via Settings > Connections > More connection settings > VPN > ADD VPN
It worked immediately while connecting my Galaxy S7 via WiFi. But if failed while connected via 3G/4G. To investigate, I did enable the firewall of my dd-wrt router (placed between my modem and my NAS) and configured it to send all its firewall messages to the syslog server of my Synology (the “Log Center”). I those logs, I found packets corresponding most probably to the VPN requests from my Galaxy S7 (They were only arriving when I was trying to establish a connection). Those were not coming from my Galaxy S7’s IP. Instead, they were coming from another Proximus IP, with a protocol 47 (Generic Route Encapsulation)?! Could this be due to Proximus configuring my profile to use CGN (Carrier Grade NAT)? Unfortunately, I couldn’t check and reconfigure this myself as the option is not available anymore via the MyProximus administration interface…
So, I decided to give up with this PPTP VPN and use a more secure but less performant VPN: L2TP/IPSEC with a PSK (IPsec pre-shared key). And miracle, after opening and routing the UDP ports 500, 1701 and 4500, it worked !
![]()
Leave a Reply